
Kubernetes Security best practices
Read time: 5 mins
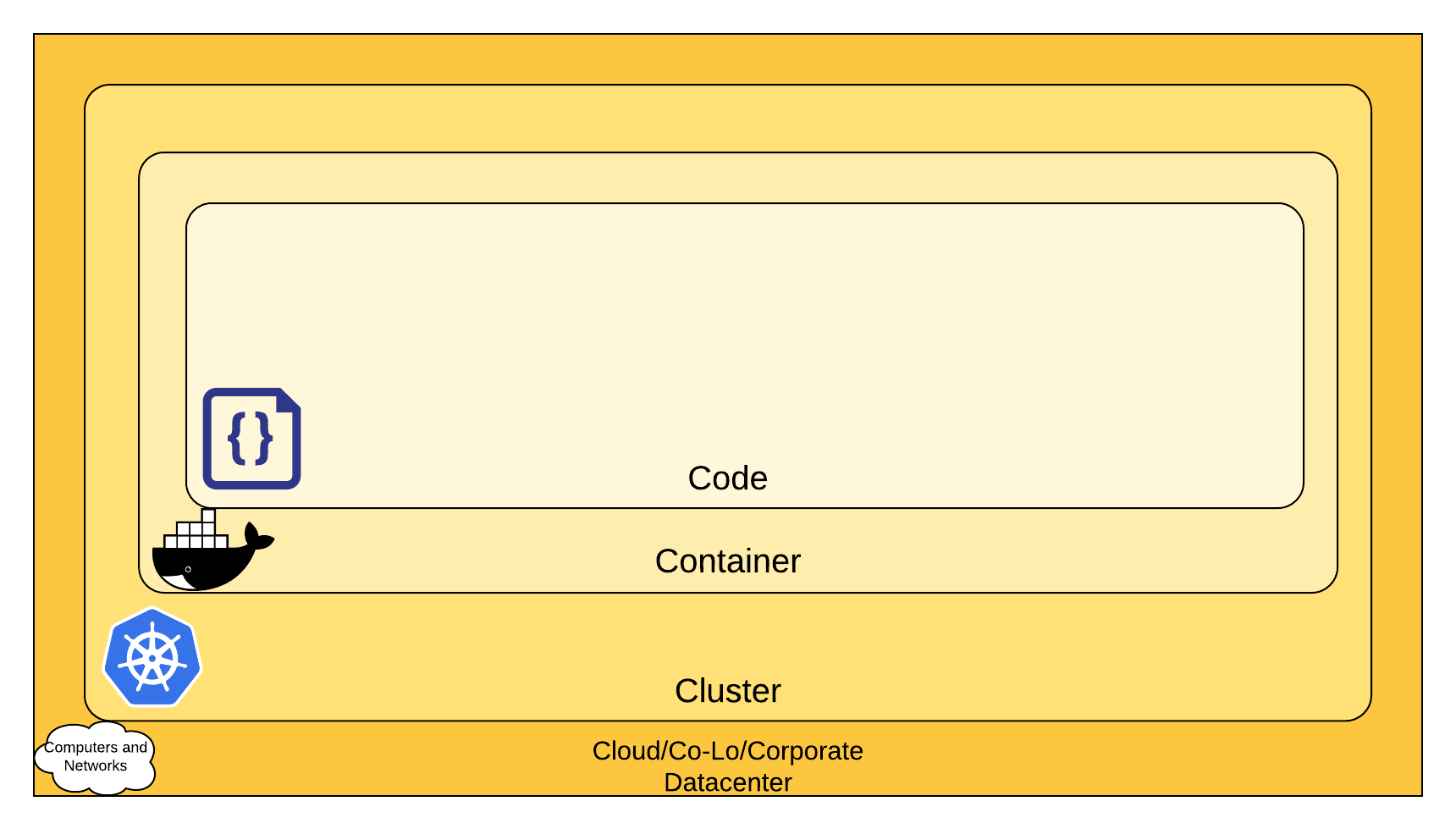
Kubernetes is an open-source container orchestration platform that helps automate the process involved in deploying, scaling, and managing containerized applications.
Security is a top priority and should be implemented at all stages of the development process. It is a critical component of configuring and maintaining clusters and applications aligned to the lifecycle – build, ship, run, and deployment. Staying ahead of security risks can be a difficult task, but implementing multiple layers of defense can reduce the overall risks attached.
A few months back, the Kubernetes flaw was discovered, enabling attackers to exploit clusters through the Kubernetes API server, allowing them to perform malicious activity.
Another Organization also suffered a complex cryptocurrency mining malware caused due to a misconfiguration in the Kubernetes console. One of the Kubernetes console was not password protected which the attackers took advantage of it, and they accessed the pods in the AWS environment.
Organizations worldwide are adopting Kubernetes and with the rise in popularity, security should be a concern and not an afterthought.
Best practices to secure Kubernetes are -
1. Enable Kubernetes Rule-Based Access Control (RBAC) – Define the proper access control with role-based access control and provide the right permissions to use it effectively.
2. Integrate Third-Party Authentication for API – Recommended to use OAuth 2.0to manage users and Multi-Factor Authentication to provide additional security.
3. ETCD protection with TLS, Firewall, and Encryption – Datastore access should be configured with TLS, and the access should be limited to the Kubernetes control panel. Additionally, data storage from, etc. to volumes should be encrypted.
4. Use namespaces to isolate sensitive workloads – Namespaces are the main isolation perimeter for Kubernetes resources. It helps reference network policies, access control restrictions, and security controls. It reduces the impact of mistakes and destructive actions by authorized users.
5. Use Network Policies –Control network access into and out of containerized applications. Restrict access to services within clusters and cloud’s metadata API from pods.
6. Use Process whitelisting – Images whitelisted as per the organization’s policy is strictly recommended.
Private registries can be used to store and push approved images, it narrows the field and reduces the potential risk.
7. Enable Audit Logging – Logging should be enabled and all malicious and unwanted API calls needs to be monitored. Notifications on authorization failure where the attacker tries to use the stolen credentials also need to be set up.
8. Continuous Security Vulnerability Scanning – Containers may include known vulnerabilities and a continuous assessment ensures required security posture.
9. Keep Kubernetes version up to date – Source images should constantly be updated. The rolling updates feature gradually updates the running application by upgrading its images to the latest version.
10. Secure the Kubelet – Misconfiguring kubelet in the primary node agent running on each node exposes to backdoor access. Disable anonymous access as false and set ports to read-only.
Zensar provides out-of-the-box solutions for continuous protection and security of your Kubernetes environment.



