Threat Protection
Threat Protection
Our unique methodology combined with core offensive security-trained talent brings the best of both worlds, where you get the most comprehensive details of hidden gaps in your infrastructure as well as fast detection and mitigation of threats.

Threat Protection

Our unique methodology combined with core offensive security-trained talent brings the best of both worlds, where you get the most comprehensive details of hidden gaps in your infrastructure as well as fast detection and mitigation of threats.
Why is threat protection so important?
Threat protection service offerings
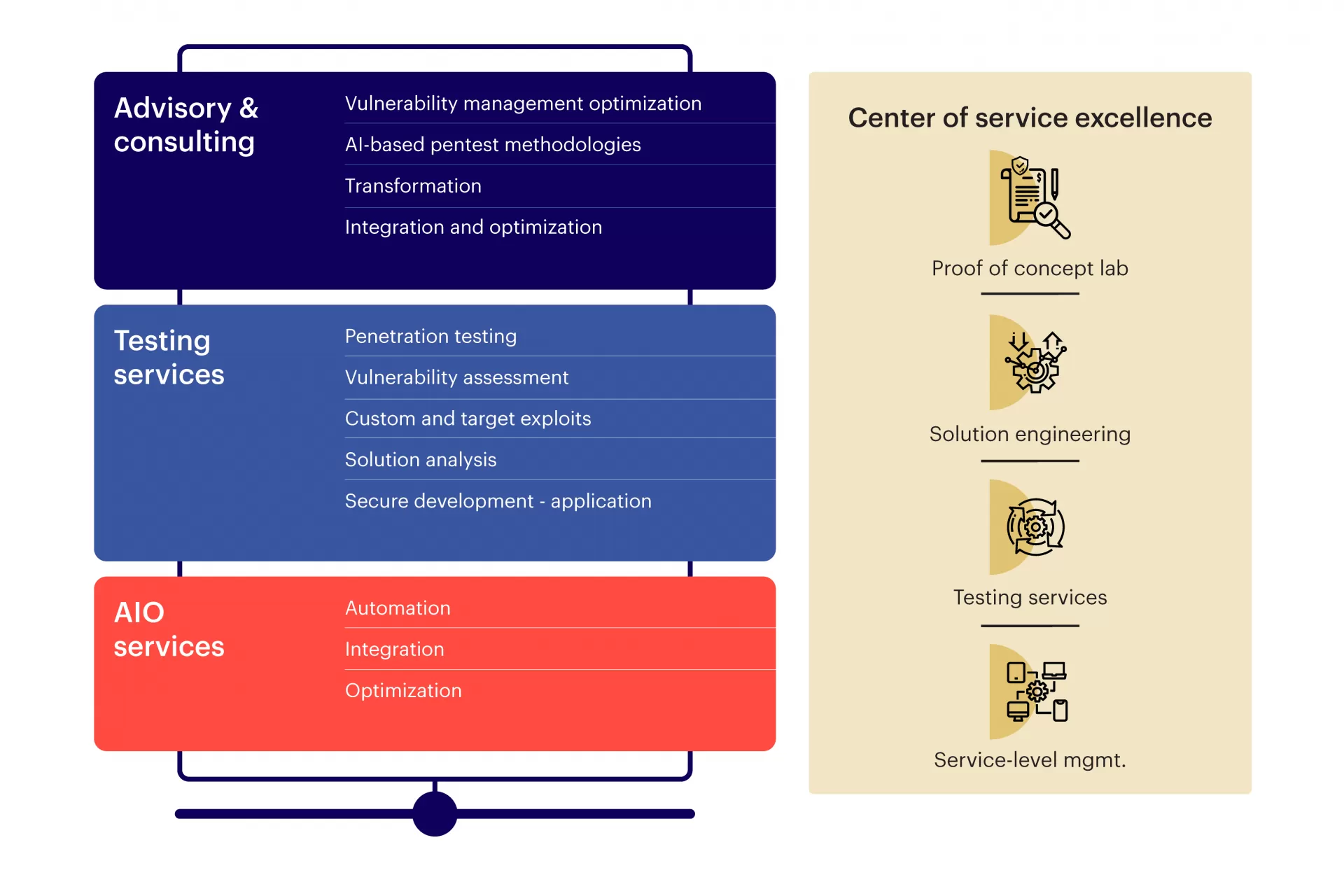
Our capabilities
Digital Security Offerings
Our experience
Explore other offerings

Intelligent Hybrid Infrastructure Services
Drive operational efficiency with human smarts backed by machine intelligence
Take me there
Digital Security
Protect data, networks, and devices from malicious programs and build better digital resilience
Take me there









